vendure-data-hub-plugin
Secrets Management
Secrets store sensitive values like API keys, passwords, and tokens securely.
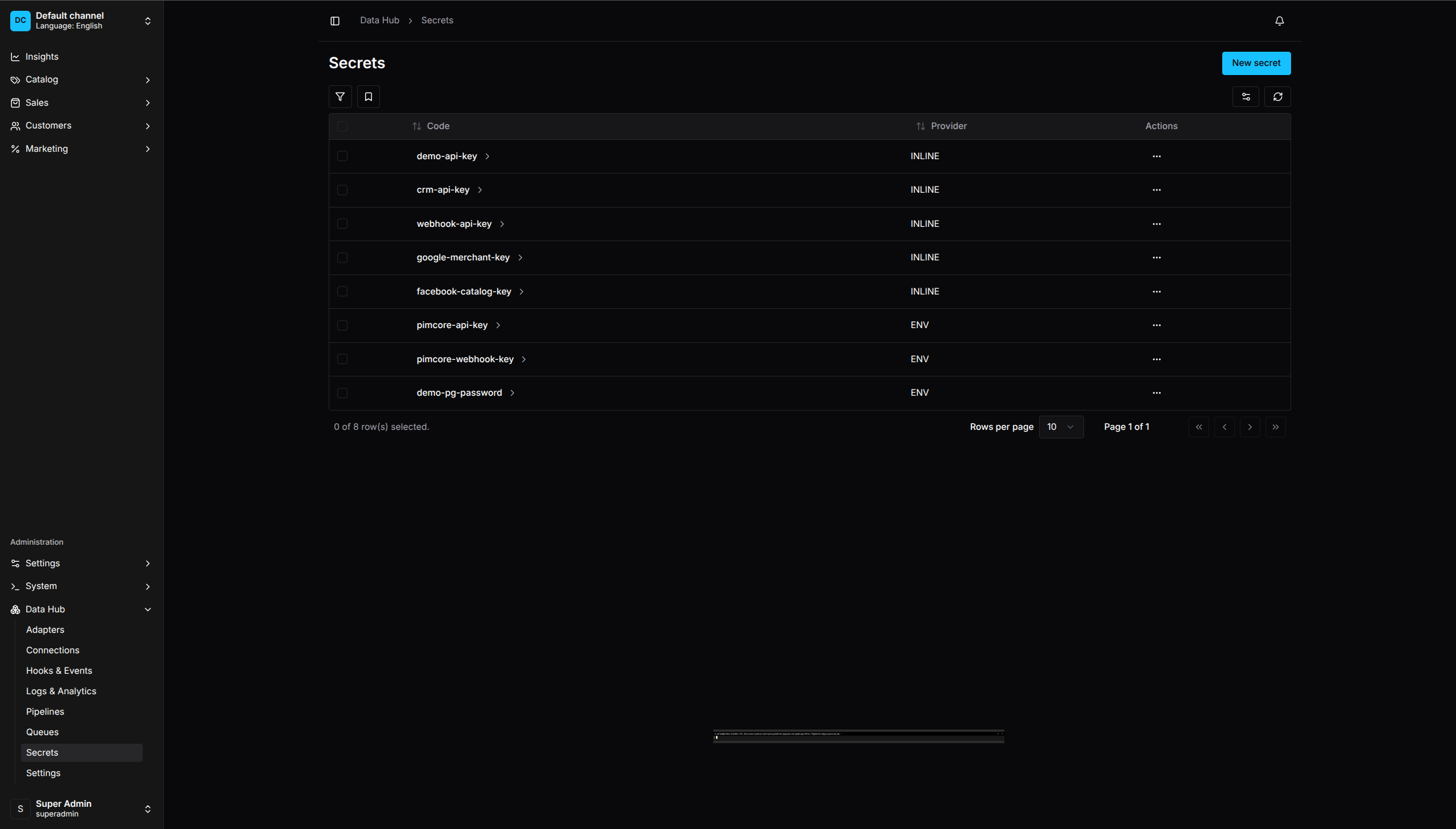
Secrets List - Manage API keys, passwords, and tokens
Why Use Secrets
- Security - Values are encrypted at rest
- Auditability - Access is logged
- No Exposure - Values never appear in logs or API responses
- Centralized - Update credentials in one place
Creating a Secret
- Go to Data Hub > Secrets
- Click Create Secret
- Enter:
- Code - Unique identifier
- Provider - How the value is stored
- Value - The secret value or environment variable name
- Click Save
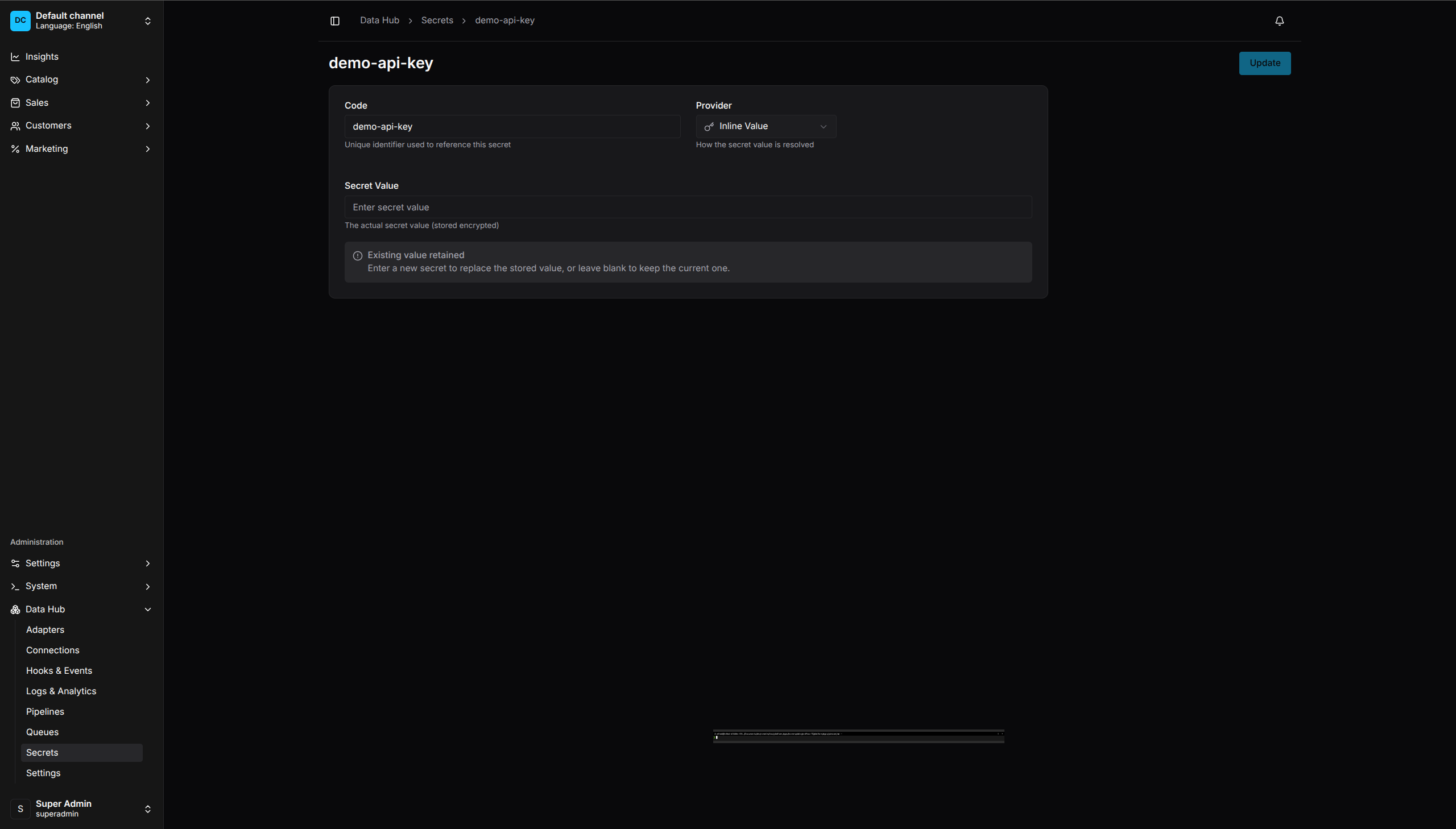
Secret Configuration - Encrypted storage with provider options
Secret Providers
Inline
Store the value directly in the database (encrypted):
Code: api-key
Provider: inline
Value: sk_live_abc123...
Best for: Development, testing, values that rarely change.
Environment Variable
Read the value from an environment variable:
Code: api-key
Provider: env
Value: SUPPLIER_API_KEY
The Value field contains the environment variable name, not the actual secret. The value is read at runtime.
Best for: Production, CI/CD pipelines, Docker deployments.
Using Secrets in Pipelines
Reference secrets by code in step configurations.
HTTP API Authentication
Bearer token:
.extract('api-call', {
adapterCode: 'httpApi',
url: 'https://api.example.com/products',
bearerTokenSecretCode: 'api-key',
})
Basic auth:
.extract('api-call', {
adapterCode: 'httpApi',
url: 'https://api.example.com/products',
basicAuthSecretCode: 'api-credentials', // Format: username:password
})
API key header:
.extract('api-call', {
adapterCode: 'httpApi',
url: 'https://api.example.com/products',
apiKeySecretCode: 'api-key',
apiKeyHeader: 'X-API-Key',
})
Database Passwords
// In connection configuration
{
code: 'erp-db',
type: 'postgres',
settings: {
host: 'db.example.com',
database: 'erp',
username: 'vendure',
passwordSecretCode: 'erp-db-password',
},
}
S3 Credentials
{
code: 'aws-storage',
type: 's3',
settings: {
region: 'us-east-1',
accessKeyIdSecretCode: 'aws-access-key',
secretAccessKeySecretCode: 'aws-secret-key',
},
}
SFTP Passwords and Keys
{
code: 'supplier-ftp',
type: 'sftp',
settings: {
host: 'ftp.supplier.com',
username: 'vendure',
passwordSecretCode: 'sftp-password',
// Or for key-based auth:
privateKeySecretCode: 'sftp-private-key',
},
}
Viewing Secrets
- Go to Data Hub > Secrets
- The list shows secret codes and providers
- Values are never displayed
Editing Secrets
- Click on a secret
- Update the provider or value
- Click Save
Note: You cannot view the existing value when editing.
Deleting Secrets
- Click the menu (⋮) on a secret
- Select Delete
- Confirm deletion
Warning: Deleting a secret will break any pipelines or connections using it.
Secret Rotation
To rotate a secret:
- Create a new secret with the new value
- Update pipelines/connections to use the new secret code
- Test the updated configuration
- Delete the old secret
Or, update the secret value directly:
- Edit the secret
- Enter the new value
- Save
All pipelines using that secret will use the new value immediately.
Code-First Secrets
Define secrets in your Vendure config:
DataHubPlugin.init({
secrets: [
// From environment variable
{ code: 'api-key', provider: 'ENV', value: 'SUPPLIER_API_KEY' },
// Inline value (not recommended for production)
{ code: 'test-key', provider: 'INLINE', value: 'test-value' },
],
})
Code-first secrets:
- Are synced to the database on startup
- Take precedence over UI-created secrets with the same code
- Appear as read-only in the UI
Security Best Practices
Use Environment Variables in Production
{ code: 'api-key', provider: 'ENV', value: 'API_KEY' }
This keeps secrets out of your codebase and allows different values per environment.
Principle of Least Privilege
- Use separate secrets for different systems
- Create read-only API keys when possible
- Use scoped tokens with minimum required permissions
Regular Rotation
- Rotate secrets periodically
- Rotate immediately if compromised
- Use the rotation workflow above
Audit Access
- Review who has
ReadDataHubSecretpermission - Monitor secret access in logs
- Limit secret management to administrators
Never Log Secrets
The plugin is designed to never log secret values. If you’re extending the plugin, maintain this practice.